Most software still assumes the user is a person sitting in front of a screen.
That assumption is starting to break.
A growing wave of products is being built around a different primary user: the agent. Not the human operator. Not the admin. Not even the developer wiring up the workflow. The software worker itself.
That sounds like a small shift in framing. It isn’t.
When the user is an agent, product design changes fast. You stop caring so much about menu polish, onboarding tours, visual persuasion, and habit loops. You start caring about APIs, reliability, machine-readable state, permission boundaries, audit trails, retries, and recovery.
That’s why the current burst of so-called agent infrastructure is more interesting than it first appears. Under the noise, a real category is taking shape.
What makes a tool agent-first?
A tool becomes agent-first when it is designed around the operational needs of autonomous software.
In practice, that usually means 5 things.
1. Programmatic identity
The agent can get its own inbox, phone number, wallet, browser session, or execution environment.
2. Actionable interfaces
The product exposes APIs, structured outputs, or machine-native workflows instead of assuming a human will click through a dashboard.
3. Persistent context
The agent can hold memory, credentials, state, and continuity across sessions.
4. Governed autonomy
There are real controls around permissions, spending, reputation, and accountability because the agent is expected to act, not just suggest.
5. Operational reliability
The tool is optimized for repeatable execution, not engagement.
That last point is the deepest one.
Once agents become actual users, product teams stop optimizing for attention and start optimizing for successful task completion.
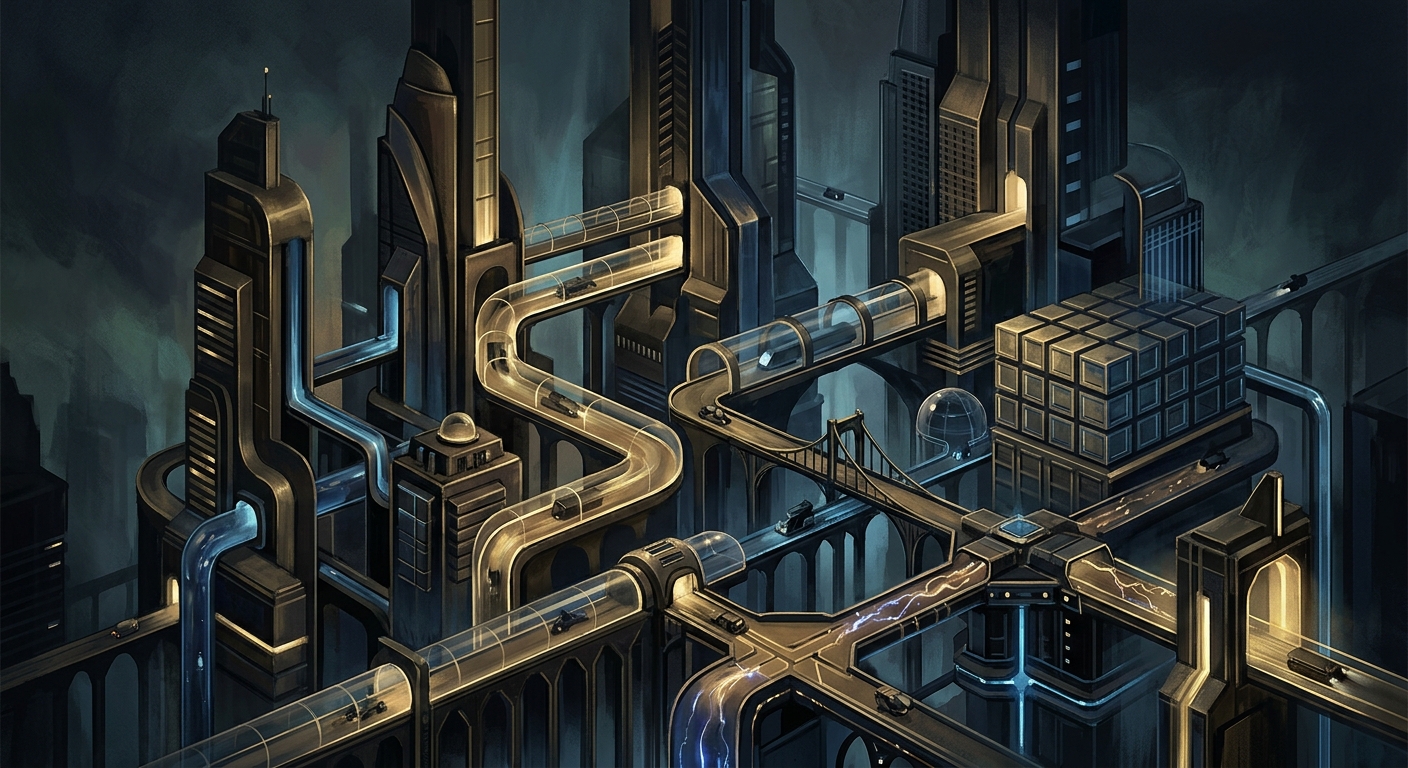
The stack is starting to look like a digital employee kit
The cleanest way to understand this market is to look at the primitives founders are trying to assemble.
Individually, some of these look narrow or gimmicky. Together, they start to resemble the operating kit for a digital coworker.

An emerging software stack for agents: identity, execution, browsing, memory, payments, and trust.
1) Identity and communications
Some of the earliest agent-first tools are trying to give software workers the boring but necessary organs of business communication.
That includes things like:
- AgentMail, so agents can have email accounts
- AgentPhone, so agents can have phone numbers, SMS, and voice
- Kapso, so agents can use WhatsApp numbers
- Linq, mentioned in the thread as a way for agents to use iMessage
- Clawphone, surfaced in replies as another phone-like layer
At first glance, this category feels a little silly.
Why would an agent need an email address or a phone number?
The answer is simple: because the world still runs on human interfaces.
Businesses still use email. Customers still answer phones. Vendors still confirm actions over SMS. Plenty of workflows still pass through inboxes, forms, and messaging channels built for people.
So even if these products are transitional, they still matter.
Critics of the category made a fair point in the X thread. Some argued that email addresses and phone numbers are just temporary hacks, legacy human-era wrappers around what should eventually become agent-to-agent protocols.
I think that’s probably right.
But transitional infrastructure can still become very large businesses. Plenty of huge companies were built by helping one computing era interface with the previous one.
2) Compute and execution environments
If agents are going to do meaningful work, they need somewhere to live.
This is one of the cleanest agent-first categories because the need is obvious.
Agents need:
- persistent execution
- resumability
- filesystem access
- secret isolation
- elastic compute
- bounded permissions
That’s where tools like these fit:
- Daytona
- E2B
- other runtimes mentioned in replies that emphasize long-running sessions, secret security, and burstable CPU or RAM for heavier tasks
A chatbot tab is not enough. If an agent is going to actually operate, it needs a workstation layer.
That workstation might be a sandbox, a cloud runtime, a persistent container, or something closer to a software employee desktop. The packaging will vary. The core need will not.
3) Browsers, web crawling, and the messy real internet
A ridiculous amount of business workflow still lives inside websites.
That means the browser layer is being rebuilt too.
Tools repeatedly cited in and around the thread included:
- Browserbase
- Browser Use
- Hyperbrowser
- Revyl, for navigating and testing mobile apps
There is also a separate but related category built around skipping the browser when possible:
- Firecrawl, for machine-friendly crawling and extraction
This split matters.
Sometimes the best tool for an agent is a browser. Sometimes the best tool is the product that helps the agent avoid using a browser at all.
That’s a useful lens for evaluating the category. Every click an agent has to simulate is a tax. Every workflow that can be replaced with a clean API or structured extraction surface is a quality improvement.
4) Memory, search, and retrieval
If an agent cannot remember, it is not a coworker. It is a goldfish with a shell command.
That’s why memory and retrieval products keep appearing near the center of this conversation.
Examples include:
- Mem0, for persistent memory
- Exa, for web search that works better for programmatic agents than traditional search interfaces do
- Sixtyfour, for people and company search
This is one of the places where the human-first stack breaks most obviously.
Human note-taking apps are not agent memory systems.
Consumer search engines are not optimized for software trying to gather evidence, rank sources, and keep a traceable working set. Agents need retrieval systems that are structured, inspectable, and easy to wire into decision loops.
That’s a different product problem.
5) Tool use, APIs, and integration surfaces
Another large slice of the category is about helping agents actually do useful work across the rest of the software economy.
That includes:
- Composio, for SaaS tool access
- Orthogonal, for easier API access
- generated API layers that make existing services more machine-usable
- MCP, increasingly treated as a standard way for models and agents to discover and use tools
This layer might end up being one of the most defensible.
Agents usually don’t fail because they can’t speak.
They fail because real systems are fragmented, stateful, permissioned, inconsistent, and full of annoying edge cases. The more a company can absorb that complexity into a stable machine-facing contract, the more valuable it becomes.
6) Voice, payments, and commercial action
Once agents move from assistant mode into operator mode, they need ways to communicate and transact.
That’s where another cluster of agent-first products starts to matter:
- ElevenLabs and Vapi, for voice interfaces
- Kite and Sponge, for payments
- Reins, mentioned as a bank-account-like primitive for agents
- x402 / AP2, discussed in adjacent X posts as machine-native payment rails for HTTP-level transactions
This part of the stack feels early, but it’s hard to imagine the category maturing without it.
If an agent can search, browse, schedule, and call tools but cannot pay, it is still missing one of the key behaviors needed to complete end-to-end economic workflows.
The second agents start spending money, a new question dominates the whole category.
Can they be trusted?
The primitives are multiplying faster than the trust and orchestration layers that hold them together.
The missing center of gravity is trust
The most insightful replies in the thread were not the ones adding more point solutions.
They were the ones pointing at the missing layer.
Again and again, people converged on the same idea: identity, trust, permissions, compliance, and reputation are still underbuilt.
Examples mentioned in the thread and adjacent discussion included:
- AgentProof, for reputation
- Skyfire, for verified agent identity and trust
- proposals around agent passports, machine-speed compliance, and track records
- on-chain identity and reputation concepts like ERC-8004
This is where the category stops being cute.
A useful agent can already browse, call APIs, remember things, and maybe even pay for services. But before companies let agents operate with real authority, they need answers to some very unsexy questions:
- Who owns this agent?
- What permissions does it have?
- What systems can it touch?
- What is it allowed to spend?
- What has it done before?
- How do I revoke it?
- How do I audit it after something goes wrong?
The trust layer may end up mattering more than any single memory, browser, or integration product.
It’s also the layer that feels most likely to consolidate value.
The strongest critique, and why it still doesn’t kill the category
The best skeptical reply in the original thread argued that many of these products will be dead within 12 to 18 months because agents do not fundamentally need email addresses or phone numbers.
Humans need agents to have those things because we haven’t built anything better yet.
That’s a smart critique.
I think it’s directionally correct.
A lot of today’s agent-first tooling probably is temporary. Some categories are scaffolding for the transition, not permanent infrastructure.
But that does not make the whole category fake.
It just means there are two different opportunities hiding inside it.
The first is the transitional opportunity: help agents work inside the human-built software world that already exists.
The second is the native opportunity: build machine-first protocols, trust layers, payment rails, and execution surfaces that make the old human wrappers less necessary over time.
Both can be valuable. One may simply age better than the other.
The deeper shift: from UX-first software to contract-first software
The real story here is not that AI agents need more toys.
The real story is that software is being redesigned around non-human operators.
That changes what good product design means.
For a human-first product, you might optimize for:
- visual polish
- onboarding flows
- persuasion
- attention retention
- habit loops
- conversion paths
For an agent-first product, the priorities start looking more like this:
- API reliability
- deterministic behavior
- predictable auth
- machine-readable outputs
- latency
- retry behavior
- structured permissions
- observability
- auditability
- recovery logic
That is a different product religion.
It also explains why so many of these companies feel infrastructural even when they are solving familiar business problems. They are rebuilding existing software categories around a different user model.
More tools that fit the pattern
Looking beyond the original thread, the broader agent-first bucket already seems to include adjacent tools like:
- Bool, for helping agents spin up websites
- Revyl, for mobile navigation and testing
- Skyfire, for identity and trust
- x402 / AP2, for agent-native economic rails
- Reins, for financial primitives
- MCP-compatible tool servers, which turn software capabilities into machine-discoverable surfaces
- runtimes like OpenClaw, which package execution, integrations, scheduling, and control around agents as active operators
Not all of these will win.
Plenty will disappear.
But they do share a worldview: the software user is no longer assumed to be a person.
That is the pattern worth paying attention to.
What happens next
I think the durable winners in this category will do 1 of 3 things well.
1. Replace human-facing wrappers with machine-native primitives
These companies remove inbox cosplay and browser gymnastics, then expose cleaner interfaces agents actually want.
2. Own the trust and control plane
These companies handle identity, permissions, policy, compliance, spending controls, and auditability across fleets of agents.
3. Orchestrate the stack
These companies become the glue.
They decide which tool gets called, in what order, with what context, under what policy, and with what fallback logic when something breaks.
That orchestration layer came up repeatedly in the replies for a reason. The primitives are multiplying faster than the systems that can coordinate them.
Why this category matters now
A lot of AI writing still treats agents as if they are mostly demos with nicer wrappers.
That misses what is changing underneath.
The practical question is no longer just whether a model can call a tool.
The practical question is whether software can be built around a user that is autonomous, machine-speed, permissioned, stateful, and non-human.
That has implications far beyond today’s startup list.
If agent-first design becomes normal, then every existing software category gets re-evaluated through a new lens:
- what does identity look like?
- what does billing look like?
- what does trust look like?
- what does UX look like when the user does not have eyes?
- what does support look like?
- what does analytics look like?
- what does compliance look like?
That is not a feature wave.
It is a worldview shift.
Final thought
The interesting thing about agent-first tools is not that they make AI feel more human.
It’s that they force software to admit that the next important user may not be human at all.
That means less emphasis on persuasion, more emphasis on execution.
Less UI theater, more operational truth.
That feels like a real category to me.
Maybe half the companies in the current crop disappear. Probably more.
But the design pattern is not going away.
Software is starting to rebuild itself around agents as first-class users.
And once you see that, a lot of the market starts to make more sense.
Sources
This post was informed by:
- Shiv Sakhuja’s X thread on agent-oriented primitives and the visible reply thread
- related X discussion surfaced through Bird around Browserbase, Firecrawl, agent payments, trust infrastructure, and orchestration
- the recurring themes across those posts: reliability over engagement, orchestration as glue, and trust as the missing layer
